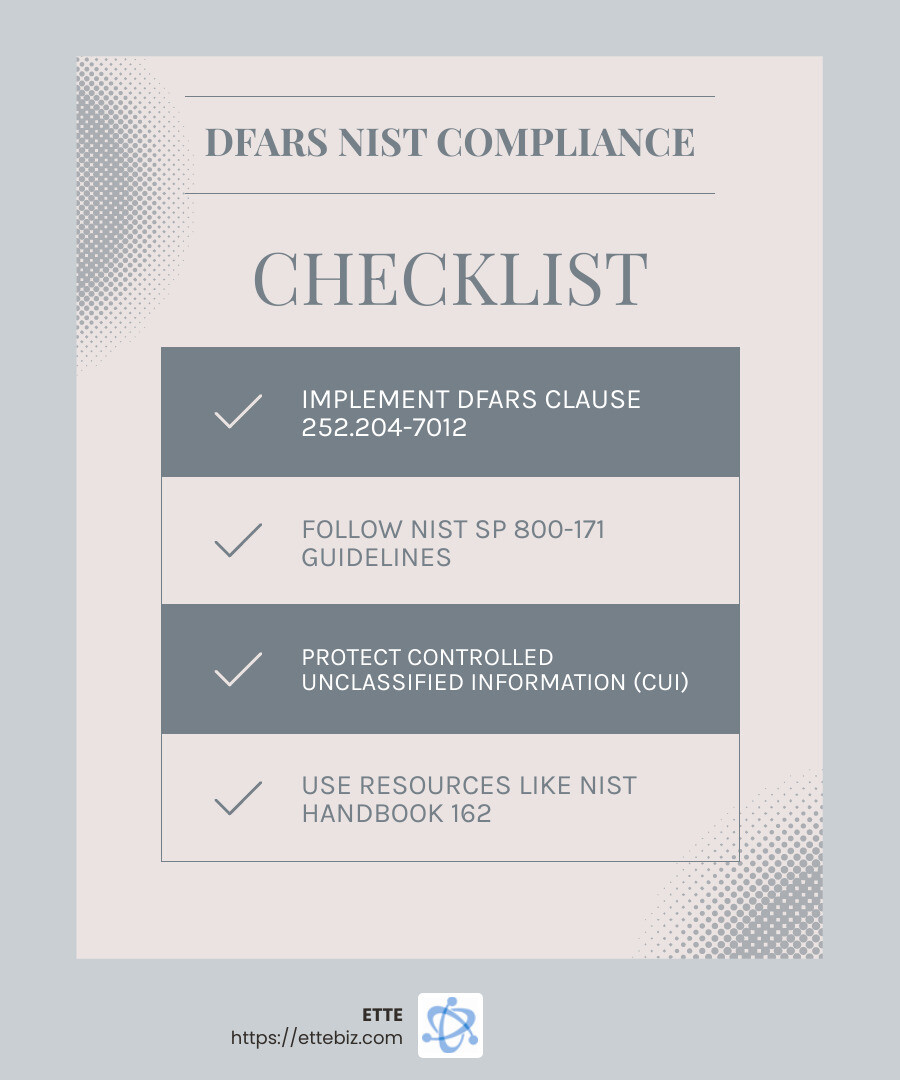
DFARS NIST compliance is essential for organizations navigating the defense industry, especially if they handle Controlled Unclassified Information (CUI). Here’s a quick overview:
- Understand Regulations: DFARS governs how defense contractors protect sensitive information, while NIST SP 800-171 offers a detailed framework of security controls to achieve compliance.
- Protect Your Data: Safeguarding CUI is crucial, and these standards ensure you have robust cybersecurity measures in place.
- Meet Requirements: Implementing NIST SP 800-171 standards is mandatory for securing DoD contracts and demonstrating your commitment to cybersecurity.
Navigating DFARS and NIST SP 800-171 can seem daunting at first. These standards are not just bureaucratic hoops to jump through; they are vital for ensuring the security and integrity of sensitive information. At the core, DFARS lays out the requirements for defense contractors in safeguarding data, while NIST SP 800-171 provides the specific security practices and controls to follow. Combined, they form the bedrock of cybersecurity compliance within the defense sector.
Given the era of cyber threats, having these systems in place isn’t just about compliance—it’s about protecting your organization from potential breaches and maintaining a competitive edge. Whether you’re a small non-profit in Washington, DC, or a major player in the defense industry, understanding these standards is critical to staying secure and competitive.
Explore more about dfars nist compliance:
– dfars and nist 800 171
– nist sp 800 171 requirements
– nist requirements for government contractors
Understanding DFARS and NIST Compliance
What is DFARS?
The Defense Federal Acquisition Regulation Supplement (DFARS) is a set of rules that defense contractors must follow. It’s like a rulebook for how to protect sensitive information when working with the Department of Defense (DoD). If you’re a defense contractor, following these rules is not optional—it’s required to secure DoD contracts.
DFARS compliance is all about making sure that sensitive data, known as Controlled Unclassified Information (CUI), is protected. This information might not be classified, but it’s still important to keep it safe from cyber threats. For example, technical data or export-controlled information falls under CUI.
The key DFARS regulation is Clause 252.204-7012. It requires contractors to implement the security controls outlined in NIST SP 800-171. This ensures that your systems are equipped to handle and protect CUI effectively.
What is NIST SP 800-171?
NIST SP 800-171 is a special publication by the National Institute of Standards and Technology. It provides a detailed framework of security requirements that organizations must follow to protect CUI in non-federal systems.
Think of NIST SP 800-171 as a checklist of security measures. It includes things like access controls, encryption, and incident response plans. By following these guidelines, organizations can safeguard their systems from cyber threats.
Conducting a Basic Assessment is the first step in achieving NIST compliance. This self-assessment helps you understand your current cybersecurity posture and identify any gaps in your security controls. For more rigorous evaluation, Medium and High Assessments are conducted by government personnel to ensure compliance with the standards.
To make the process easier, resources like the MEP National Network and the NIST Handbook 162 are available. These tools guide organizations through the complexities of compliance, helping them maximize the impact of their cybersecurity investments.
In conclusion, DFARS NIST compliance is crucial for defense contractors. It ensures the protection of sensitive information and positions your organization as a trusted partner in the defense industry. Understanding and implementing these standards not only helps in securing DoD contracts but also improves your cybersecurity posture, safeguarding your organization against potential threats.
Steps to Achieve DFARS NIST Compliance
Conducting a Basic Assessment
The journey to DFARS NIST compliance begins with a Basic Assessment. This is a self-assessment where you review your organization’s system security plan. It’s like a health check-up for your cybersecurity setup.
The goal is to identify how well your current systems align with the NIST SP 800-171 requirements. You’ll look at your policies, procedures, and technical controls. The outcome of this assessment is a score with a “low” confidence level since it’s self-generated. But don’t worry—it’s a starting point to understand where improvements are needed.
To get the most out of your Basic Assessment, consider using the NIST Handbook 162. This resource offers detailed guidance on conducting assessments and interpreting results. It’s a valuable tool for pinpointing areas that need attention.
Medium and High Assessments
Once you complete your Basic Assessment, the next steps involve more thorough evaluations: Medium and High Assessments. These are conducted by government personnel and provide a deeper dive into your cybersecurity practices.
A Medium Assessment involves reviewing your Basic Assessment and discussing any gaps with you. This results in a “medium” confidence level. For a High Assessment, the process is even more detailed. It includes verifying the implementation of security controls and can involve discussions to clarify any uncertainties.
Both assessments focus on document reviews and system checks to ensure compliance with NIST SP 800-171. They help validate that your cybersecurity measures are robust and effective.
Utilizing Resources for Compliance
Navigating the path to compliance can be challenging, but you don’t have to do it alone. Leveraging resources like the MEP National Network can make a significant difference. This network provides access to public and private sector expertise, helping organizations improve their cybersecurity posture.
Additionally, the NIST Handbook 162 is an excellent guide for conducting self-assessments. It offers practical advice on implementing NIST SP 800-171 requirements custom to your specific needs.
For those looking to streamline the compliance process, working with a cybersecurity consultant can be beneficial. They bring specialized knowledge and experience, helping you create a compliance checklist and manage assessments efficiently.
By taking advantage of these resources, you can ensure that your organization not only meets the necessary compliance standards but also strengthens its overall cybersecurity framework.
With the right strategy and support, achieving DFARS NIST compliance becomes a manageable and rewarding process.
Conclusion
At ETTE, we understand that achieving DFARS NIST compliance is not just about meeting regulatory requirements; it’s about enhancing operational efficiency and gaining a competitive edge. Our expertise in IT support and consulting services empowers organizations to steer the complex landscape of cybersecurity regulations with confidence.
Operational Efficiency
Compliance isn’t just a checkbox exercise. It streamlines your operations by identifying and mitigating risks before they become issues. With a robust cybersecurity framework in place, you can focus on what you do best—running your business efficiently. Our team at ETTE helps ensure that your systems are not only compliant but also optimized for peak performance.
Competitive Edge
Cybersecurity is a critical factor in maintaining a competitive edge. By achieving and maintaining compliance, you demonstrate to your clients and partners that you are committed to protecting sensitive information. This commitment improves your reputation and opens doors to lucrative opportunities, especially in government contracting.
Partnering with ETTE means having a dedicated team that understands the intricacies of DFARS NIST compliance. We work with you to implement effective solutions that align with your business goals. Our local presence in Washington, DC, ensures personalized support and quick response times, so you’re never alone on your compliance journey.
Explore how our NIST 800 Compliance Services can help you achieve compliance with ease. Let us be your guide in building a secure and resilient IT environment that supports your business’s growth and success.